Secure SSH Access to IoT Devices Remotely with Confidence
SSH (Secure Shell) has become an essential tool for remotely managing IoT devices. In today's interconnected world, secure remote access to IoT devices is no longer a luxury but a necessity. Whether you're a developer, network administrator, or tech enthusiast, understanding how to securely connect to IoT devices using SSH is crucial for maintaining device integrity and protecting sensitive data.
With the rapid growth of the Internet of Things (IoT), more devices are connected to the internet than ever before. From smart home appliances to industrial sensors, these devices require regular maintenance and updates. However, ensuring secure access to these devices remotely can be challenging without the right tools and protocols in place.
This comprehensive guide will walk you through the process of securely connecting to IoT devices using SSH, covering everything from basic setup to advanced configurations. By the end of this article, you'll have a solid understanding of how to implement secure remote access and download files from IoT devices without compromising security.
What is SSH and Why is it Important for IoT?
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure remote access to network devices and servers. It encrypts all data transmitted between the client and server, ensuring confidentiality and integrity. For IoT devices, SSH is particularly important because it allows administrators to securely manage devices without exposing sensitive information to potential threats.
Key Benefits of SSH for IoT:
- Encryption of all communication
- Authentication mechanisms to ensure secure access
- Support for file transfer protocols like SCP and SFTP
- Compatibility with a wide range of devices
According to a report by Gartner, the number of connected IoT devices is expected to exceed 25 billion by 2025. With such a vast number of devices online, ensuring secure remote access through SSH is critical for maintaining system integrity and protecting user data.
Overview of IoT Devices and Remote Access
Understanding IoT Devices
IoT devices encompass a wide range of gadgets, from smart thermostats and security cameras to industrial sensors and medical devices. These devices are typically equipped with embedded systems that allow them to communicate over the internet. However, their small form factor and limited resources often make them vulnerable to security threats.
Remote access to IoT devices is essential for tasks such as firmware updates, configuration changes, and diagnostic troubleshooting. Without secure access, these devices can become entry points for cyberattacks, compromising entire networks.
Challenges of Remote Access
One of the primary challenges of remote access to IoT devices is ensuring security while maintaining ease of use. Many IoT devices lack robust security features, making them susceptible to unauthorized access. Additionally, managing multiple devices across different networks can be complex without a standardized approach.
SSH addresses these challenges by providing a secure and reliable method for remote access, ensuring that only authorized users can interact with the devices.
Setting Up SSH on IoT Devices
Enabling SSH on IoT Devices
Before you can access an IoT device remotely using SSH, you need to ensure that SSH is enabled on the device. The process varies depending on the device's operating system and hardware. Below are general steps for enabling SSH on common IoT platforms:
- Linux-based Devices: Most Linux-based IoT devices have SSH pre-installed. To enable it, simply start the SSH service using the command `sudo service ssh start`.
- Windows IoT Devices: Windows IoT Core supports SSH through the OpenSSH server. You can enable it by installing the OpenSSH feature from the Windows Settings app.
- Custom Firmware Devices: For devices running custom firmware, check the device's documentation for specific instructions on enabling SSH.
Configuring SSH Settings
Once SSH is enabled, you can configure its settings to enhance security. Key configuration options include:
- Changing the default SSH port (e.g., from 22 to a custom port)
- Disabling password authentication in favor of public key authentication
- Limiting access to specific IP addresses or networks
These configurations can be made by editing the SSH configuration file, typically located at `/etc/ssh/sshd_config` on Linux-based systems.
Securing SSH Connections
Implementing Strong Authentication
One of the most effective ways to secure SSH connections is by implementing strong authentication methods. Public key authentication is highly recommended, as it eliminates the need for passwords and reduces the risk of brute-force attacks.
To set up public key authentication:
- Generate a public-private key pair using the `ssh-keygen` command.
- Copy the public key to the IoT device using the `ssh-copy-id` command.
- Disable password authentication in the SSH configuration file.
Regularly Updating SSH Software
Keeping SSH software up to date is crucial for maintaining security. Regular updates ensure that any vulnerabilities are patched promptly. Most IoT platforms provide automatic updates for SSH software, but it's always a good idea to check for updates manually.
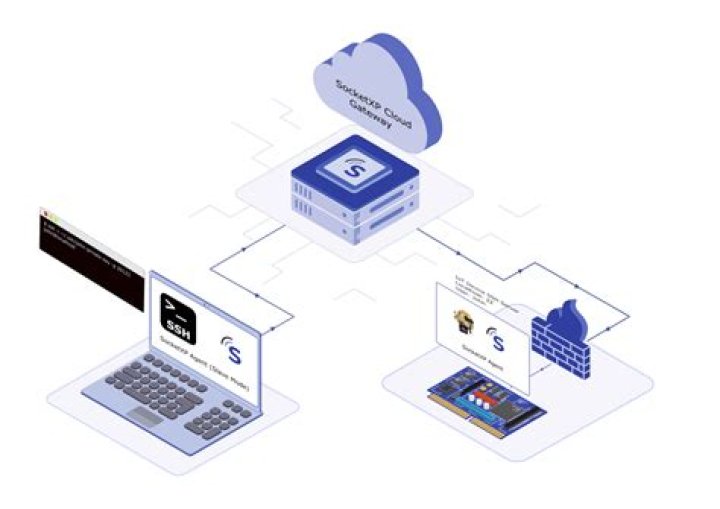
Accessing IoT Devices Remotely
Using SSH Clients
To access IoT devices remotely, you'll need an SSH client. Popular SSH clients include:
- PuTTY: A free and open-source SSH client for Windows.
- OpenSSH: A command-line SSH client available on most Unix-based systems.
- Termius: A cross-platform SSH client for mobile devices.
Each client has its own interface and features, so choose one that best suits your needs.
Connecting to IoT Devices
Once you have an SSH client installed, connecting to an IoT device is straightforward. Use the following command format:
ssh username@device_ip_address
Replace `username` with the appropriate username for the IoT device and `device_ip_address` with the device's IP address. If you've configured a custom SSH port, include it using the `-p` option:
ssh -p custom_port username@device_ip_address
Downloading Files from IoT Devices
Using SCP for File Transfer
SCP (Secure Copy Protocol) is a secure method for transferring files between local and remote systems over SSH. To download a file from an IoT device, use the following command:
scp username@device_ip_address:/path/to/remote/file /path/to/local/directory
This command copies the specified file from the IoT device to your local machine. For transferring entire directories, use the `-r` option:
scp -r username@device_ip_address:/path/to/remote/directory /path/to/local/directory
Using SFTP for Interactive File Management
SFTP (SSH File Transfer Protocol) provides an interactive interface for managing files on remote systems. To connect to an IoT device using SFTP:
sftp username@device_ip_address
Once connected, you can use SFTP commands such as `get`, `put`, and `ls` to manage files on the device.
Troubleshooting Common SSH Issues
While SSH is generally reliable, issues can arise due to misconfigurations or network problems. Below are some common SSH issues and their solutions:
- Connection Refused: Ensure that the SSH service is running and that the correct IP address and port are being used.
- Authentication Failed: Double-check the username and password or public key configuration.
- Timeout Errors: Verify network connectivity and ensure that firewalls are not blocking the SSH port.
Best Practices for SSH IoT Device Management
To ensure secure and efficient management of IoT devices using SSH, follow these best practices:
- Regularly audit SSH configurations and access logs.
- Implement network segmentation to isolate IoT devices.
- Use strong, unique passwords for all accounts.
- Limit SSH access to trusted networks or IP addresses.
Recommended Tools for SSH Access
SSH Clients
Some of the best SSH clients for managing IoT devices include:
- OpenSSH: A robust and widely-used SSH client for Unix-based systems.
- Bitvise SSH Client: A feature-rich SSH client for Windows.
- Termius: A user-friendly SSH client for mobile devices.
SSH Servers
For IoT devices, consider using lightweight SSH servers such as:
- Dropbear: A compact SSH server suitable for resource-constrained devices.
- OpenSSH: A full-featured SSH server with extensive security features.
The Future of SSH in IoT
As the IoT landscape continues to evolve, the role of SSH in securing remote access to devices will only become more critical. Emerging technologies such as quantum-resistant cryptography and zero-trust architectures are likely to shape the future of SSH in IoT.
Organizations must stay informed about these developments and adapt their security strategies accordingly to protect their IoT ecosystems from emerging threats.
Conclusion
In conclusion, securely accessing IoT devices remotely using SSH is essential for maintaining device integrity and protecting sensitive data. By following the steps outlined in this guide, you can implement secure SSH connections and efficiently manage your IoT devices.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and management.


