How to Use SSH Remote on Mac for IoT: A Comprehensive Guide
Mastering SSH remote access on your Mac can revolutionize how you interact with IoT devices. Whether you're a beginner or an experienced developer, understanding SSH will unlock countless possibilities for managing and configuring remote systems securely. This guide will walk you through the process step by step, ensuring you have all the tools and knowledge needed to connect seamlessly to IoT devices via SSH on your Mac.
SSH (Secure Shell) is a cryptographic network protocol designed to provide secure communication over an unsecured network. It's widely used in the tech industry for managing servers, IoT devices, and other networked systems. By learning how to use SSH on your Mac, you'll gain the ability to control and monitor remote devices without compromising security.
In this article, we'll explore the fundamentals of SSH, its importance in IoT applications, and provide detailed instructions on setting up and using SSH on a Mac. We'll also cover best practices, troubleshooting tips, and additional resources to help you become proficient in this essential skill.
Table of Contents
5. Securing Your SSH Connection
6. Troubleshooting Common Issues
Introduction to SSH
SSH, or Secure Shell, is a protocol that facilitates secure communication between two networked devices. It encrypts all data exchanged, making it an ideal choice for remote administration and file transfers. The primary purpose of SSH is to ensure that sensitive information, such as passwords and commands, is protected from unauthorized access.
SSH operates on a client-server model, where the client initiates a connection to the server. Once connected, users can execute commands, transfer files, and manage configurations remotely. This protocol is particularly useful in IoT environments, where devices often need to be accessed and managed from distant locations.
Key Features of SSH
- Encryption for secure communication
- Authentication mechanisms to verify user identity
- Support for various cryptographic algorithms
- Compatibility with multiple operating systems
Why Use SSH for IoT?
Using SSH for IoT offers several advantages that make it a preferred choice among developers and administrators. First and foremost, SSH ensures that all interactions between your Mac and IoT devices are encrypted, protecting sensitive data from interception. This is crucial in IoT environments, where devices often handle personal or proprietary information.
Additionally, SSH provides a robust framework for remote management. With SSH, you can easily update firmware, configure settings, and monitor device performance without needing physical access. This capability is particularly valuable for IoT deployments spanning multiple locations.
Benefits of SSH in IoT
- Enhanced security through encryption
- Efficient remote management capabilities
- Compatibility with a wide range of IoT devices
- Support for automated scripts and tools
Setting Up SSH on Mac
MacOS comes pre-installed with SSH, making it easy to set up and use. To begin, open the Terminal application, which serves as the primary interface for SSH commands. You can find Terminal in the Utilities folder within Applications.
Once Terminal is open, you can verify that SSH is installed by typing the following command:
ssh -V
This command will display the version of SSH installed on your Mac, confirming that the protocol is ready to use.
Generating SSH Keys
For added security, it's recommended to use SSH keys instead of passwords. To generate a key pair, execute the following command:
ssh-keygen -t rsa -b 4096
This command creates a 4096-bit RSA key pair. You'll be prompted to specify a location for the key and enter a passphrase for added protection.
Connecting to IoT Devices
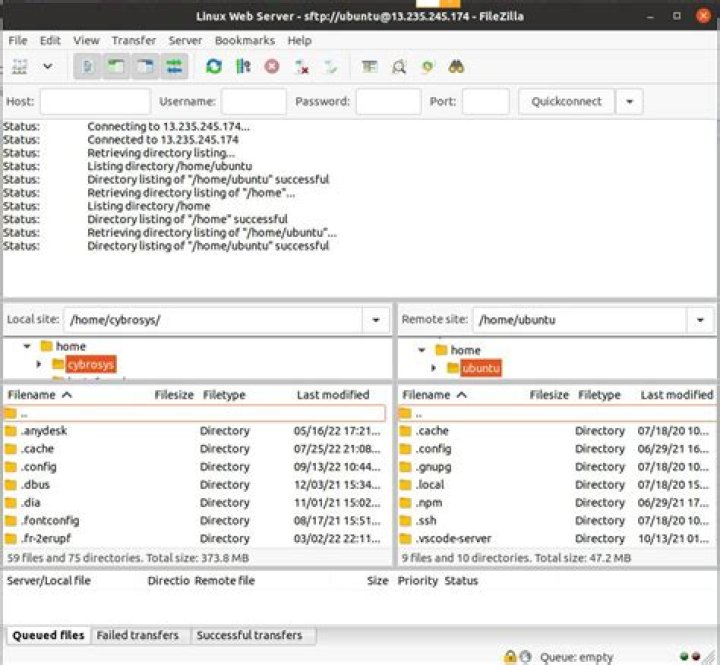
Connecting to an IoT device via SSH on your Mac is a straightforward process. Begin by identifying the IP address or hostname of the target device. This information is typically provided in the device documentation or can be obtained through network scanning tools.
Once you have the IP address or hostname, use the following command to establish a connection:
ssh username@hostname
Replace "username" with the appropriate username for the IoT device and "hostname" with its IP address or domain name. If this is your first connection to the device, you may be prompted to verify the server's fingerprint. Confirm the connection by typing "yes."
Handling Authentication
If you've set up SSH keys, the connection will proceed automatically without requiring a password. However, if you're using password-based authentication, enter the password when prompted. Remember to avoid using weak or easily guessable passwords to maintain security.
Securing Your SSH Connection
While SSH provides robust security out of the box, there are additional steps you can take to enhance the protection of your connections. One effective method is to disable password-based authentication entirely, relying solely on SSH keys. To do this, edit the SSH configuration file on the server:
sudo nano /etc/ssh/sshd_config
Locate the line that reads "PasswordAuthentication yes" and change it to "PasswordAuthentication no." Save the file and restart the SSH service for the changes to take effect.
Other Security Measures
- Use a non-standard port for SSH to deter automated attacks
- Implement firewall rules to restrict access to specific IP addresses
- Regularly update SSH and related software to patch vulnerabilities
Troubleshooting Common Issues
Even with careful setup, issues can arise when using SSH. Below are some common problems and their solutions:
Connection Refused
If you receive a "Connection refused" error, ensure that the SSH service is running on the target device. You can check this by logging into the device directly and running the following command:
sudo systemctl status ssh
If the service is not active, start it using:
sudo systemctl start ssh
Permission Denied
A "Permission denied" error usually indicates an issue with authentication. Verify that your SSH keys are correctly configured and that the server allows key-based authentication. Additionally, ensure that the username and IP address are correct.
Advanced SSH Features
Beyond basic connectivity, SSH offers several advanced features that can enhance your workflow. One such feature is port forwarding, which allows you to securely tunnel traffic through an SSH connection. This is particularly useful for accessing services behind firewalls or accessing IoT devices in remote networks.
To set up port forwarding, use the following command:
ssh -L local_port:destination_host:destination_port username@hostname
Replace "local_port," "destination_host," and "destination_port" with the appropriate values for your setup.
SSH Tunnels
SSH tunnels provide a secure way to access services on remote networks. For example, you can use an SSH tunnel to access a database or web server running on an IoT device. This method ensures that all communication is encrypted, protecting sensitive data from unauthorized access.
Best Practices for SSH
To maximize the security and efficiency of your SSH setup, follow these best practices:
- Use strong, unique passwords or SSH keys for authentication
- Regularly update SSH software and firmware on all devices
- Limit access to trusted IP addresses using firewall rules
- Monitor SSH logs for suspicious activity
Common Questions About SSH
Here are answers to some frequently asked questions about using SSH for IoT on a Mac:
Can I Use SSH Without a Password?
Yes, by setting up SSH keys, you can authenticate without entering a password each time. This method is more secure and convenient, especially for automated scripts and frequent connections.
What Should I Do If SSH Stops Working?
First, verify that the SSH service is running on the target device. Check for any recent changes in firewall rules or network configurations that might affect connectivity. If the issue persists, consult the SSH logs for more information.
Conclusion and Next Steps
Mastering SSH remote access on your Mac opens up a world of possibilities for managing IoT devices securely and efficiently. By following the steps outlined in this guide, you'll be well-equipped to connect, configure, and monitor remote systems with confidence.
To further enhance your skills, consider exploring advanced topics such as SSH automation, scripting, and integration with other tools. Additionally, stay updated on the latest developments in SSH and IoT security to ensure your systems remain protected against emerging threats.
Feel free to leave a comment or question below if you have any additional queries. Don't forget to share this article with others who may benefit from it, and explore our other resources for more in-depth guides on technology and IoT.